December 12, 2018; Boston Globe
Does your nonprofit conduct e-commerce, such as donations, event registrations, or selling items? How about allowing staff to access organization files from home or a coffee shop? Are you collecting info from subscribers or donors?
Of course, your nonprofit is doing some or all of these. That means it has become crucial for your nonprofit to step up its game around issues of cybersecurity. A recent story describing how a major international nonprofit was hacked and caught up in a $1 million cyber scam should be a wake-up call to all nonprofits.
Save the Children Federation, based in Connecticut, was fooled into sending approximately $1 million for solar panels to a project in Pakistan, a project that Save the Children supported. What happened is that one worker’s email was hacked, allowing the hacker to pose as an employee and create fake invoices. Due to insurance coverage, the organization recovered all but $112,000.
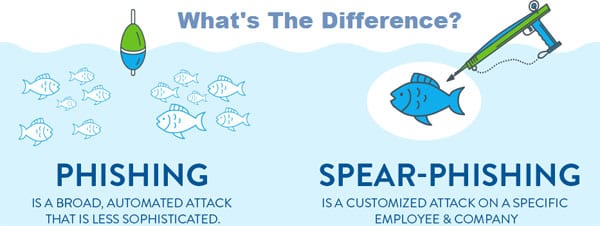
Nonprofits are no longer escaping the attention of hackers, who have learned that nonprofits often have more lax security, even when smaller dollar amounts are involved. In many of these scams, the hacker breaks in via an employee email, which has led to a term in the IT world: “PICNIC.” This acronym stands for “problem in chair, not in computer.” Translated, this means that the weak point in many security systems results from individual user actions. It can be way too easy to be scanning through a lengthy list of emails, opening and reading quickly, only to discover that what looked like an official notice from the bank or a partner business is indeed a fake email.
Sign up for our free newsletters
Subscribe to NPQ's newsletters to have our top stories delivered directly to your inbox.
By signing up, you agree to our privacy policy and terms of use, and to receive messages from NPQ and our partners.
Here are two good resources for nonprofits seeking to increase their cybersecurity:
- The State of Nonprofit Cybersecurity 2018 is a recent report from the Nonprofit Technology Network (NTEN) and Microsoft, which surveyed more than 250 nonprofits. The report shows the bright spots as well as areas needing much improvement. There were many areas explored in the report: policies, training, access, and drills/exercises, and monitoring & control. While 58 percent of respondents said their nonprofit had policies on equipment usage and data privacy, only 20 percent had documented policies in case of cyber-attack. When examining staff training regarding cybersecurity, almost 60 percent said their organization did not have any training. Staff are allowed to use their personal devices to access organization email at 70 percent of the organizations. This becomes a weak point when staff then leave their personal devices unprotected. Only 1/3 of survey respondents use a password management tool, and half of those using such management tools make its use optional.
- “Cybersecurity Resources for Nonprofits” is a website from the Federal Trade Commission. One fun thing is the list of cybersecurity quizzes. There are three: cybersecurity basics, ransomware, and vendor security quiz. See how much (or how little) you and the members of your staff know; this can create a first step in a training program, as a nonprofit’s knowledge gaps becomes apparent.
Save the Children Federation took several actions after the hack. They’ve built a system that involves the use of a second staff member to confirm all new vendors, strengthened technology systems, and put in place a requirement that a second person sign off on wire transfers.
Nonprofits cannot assume that they are exempt for cyber threats. Cyber-scams are becoming more and more common, and too many in the nonprofit world are sitting out there, largely unprotected.—Jeanne Allen